Cybersecurity is complex. Exploring different solutions and mitigating risk is important to keep an organization safe. During Cybersecurity Awareness Month, we share content to aid in understanding and using Enterprise Security Architecture.
Increasing threats, shifts in legal requirements, and cyberattackers’ improving creativity all take a toll on companies worldwide. The cost of faulty security is increasing; IBM’s annual Cost of a Data Breach Report found the average data breach cost reached an all-time high, averaging $4.35 million, and rose by 2.6% in the last year.
To avoid potentially critical situations, companies must keep their systems up-to-date, from the cloud environment to new technologies or all employee hardware. Many companies lack the capacity to plan cybersecurity internally and instead turn to security experts like mnemonic to help them set up their security plans.
What Are the Challenges and Benefits of Implementing Enterprise Security Architecture?
mnemonic aims to help clients find the best solution for their unique situations. Using their mnemonic Enterprise Security Architecture (mESA) framework, customers can understand what threats and challenges they face today and what the future holds.
By leveraging Ardoq’s partnership model, mnemonic builds Enterprise Security Architecture for their customers and themselves. Ardoq empowers organizations to use a holistic approach and visualize the business value of cybersecurity. In addition, the tool improves time to value in projects and enables higher-end customer engagement.
“Bringing structure to the intangible, we solve the real-world cybersecurity challenges our clients are facing today and expect to face tomorrow.”
- Angel Alonso, Team Leader, Governance, Risk & Compliance at mnemonic
So, what are the challenges and benefits of implementing an enterprise security architecture? While each business has unique security needs, they also share some common challenges regarding their cybersecurity. mnemonic has identified the five most common issues that, generally speaking, companies face when it comes to keeping their systems safe:
- Choosing controls
- Mitigating risk
- Supporting the business
- Using capabilities
- Optimizing security investment
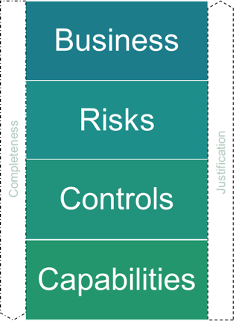
To tackle these concerns, mnemonic has developed a solution for each that follows the mESA framework - see image below. Organizations that wish to understand how Enterprise Security Architecture can help to mitigate security problems and overcome these challenges should read on.
1. Getting Started: Choosing Controls
The security sector is full of frameworks, standards, and practices, and customers often ask which they should use. The answer to their dilemmas might not be straightforward because many factors are at play, meaning each company must decide what is most relevant to them.
Instead of creating traditional Excel spreadsheets to list hundreds of controls, mnemonic uses Ardoq to present a clearer picture of common cybersecurity best practices, frameworks, and standards. The resulting picture, or map, shows the standard framework recommendations broken down into categories and subcategories, making comparison easy.
Visualizing the Control Layer
mnemonic’s Enterprise Security Architecture overview of common cybersecurity standards allows customers to see how controls relate to each other, making the framework flexible and extendable to support many different requirements. For example, when assessing the customer’s digital security maturity, automatic calculations are made based on the pipeline or, if needed, estimated by calculated fields, thus allowing companies to gain insight into how their security controls align with their different requirements.
The Control Layer digs into the control measures and objectives. For example, an objective might be to detect malicious code. The Control Layer gives everyone a choice of the many possible standards that help to reach this objective best. Because everything is mapped out in Ardoq, it's easy for mnemonic to see their choices and quickly identify how best to meet their objectives.
2. Mitigating Risk
Risks are everywhere, so it’s key to understand which ones will affect the organization. As the security market evolves, regulations and standards change. Keeping on top of the latest developments means companies can make informed decisions about where to invest in risk mitigation. But what does this mean in practice? How can risk be calculated qualitatively or quantitatively?
According to the Cloud and Security Challenges in 2022 survey report, monitoring, measuring, and reporting risk is a complex undertaking for organizations. mnemonic helps customers understand their risks and enables them to make decisions that focus on the important ones.
Breaking Down the Risk Layer With mnemonic Enterprise Security Architecture
mnemonic takes a risk-based approach, usually identifying the organization's highest risk. The upside of this method is that it allows the company to focus its resources within an increasingly complex IT ecosystem.
The Risk Layer outlined in mESA contains three components that help break down and focus actions to help mitigate risk:
- Threat events
- Several threat events can negatively impact an organization’s objectives. For example, ransomware is one of the most common threats organizations face today.
- Threat actors
- Threat events can potentially be performed by a set of threat actors, e.g., crime syndicates.
- Adversary techniques
- Threat actors use specialized techniques. These adversary techniques are categorized based on their sophistication, motivation, and resources.
mnemonic uses Ardoq to map the most relevant threat events their customers are concerned about, incorporating the relevant threat actors and the different adversary techniques these actors are known for using. Specifically, mnemonic’s threat intelligence team builds these threat events using MITRE ATT&CK techniques, mapping out the methods commonly used by malicious actors and identifying and building mitigations to help an organization reduce these potential threats.
3. Supporting the Business
In some organizations, security people are sometimes perceived as the ‘no’ people who shoot down ideas. In addition, misunderstandings can occur if IT, security, and business departments have their own ‘language’ and focus areas, which means communication across the company can sometimes be patchy. Mnemonic helps customers to build a common security language and to communicate in business terms.
Aligning All Languages With the Business Layer
For enterprise security architects to be business enablers, they must understand what the business is trying to achieve and its objectives. Security can only define how to support and enable business and bring demonstrable value to security initiatives. Nevertheless, breaking the language barrier between business and security is vital so organizations can understand how security impacts their work.
To communicate more clearly, mnemonic has defined three components that Enterprise Security Architecture can map out. When businesses see this information, they better understand how security supports and enables business.
- Business objectives - show what the business wants to achieve. For example, meeting a client’s expectations, delivering a service, and producing shareholder value.
- Business drivers for security - define the security perspective in words that the business understands. For example, build organizational resilience and exploit new technologies.
- Attributes - provide the link between security and business by modeling business drivers, for example, the CIA triad: confidentiality, integrity, and availability.
4. Using Capabilities More Effectively
Today’s security market has many vendors, so many that a business could find itself using multiple providers for the same function or paying for services they don’t need. mnemonic helps customers map out their current security capabilities. Once they know what they have, they can identify the missing security capabilities and take appropriate action to defend against these specific risks.
Build an Efficient Capabilities Portfolio
By connecting the necessary services to the technology and vendors, it’s possible to build an efficient portfolio and avoid wasting resources on several technologies that do the same job.
By seeing the Capability Layer mapped out, customers can make informed decisions on what is best for their company. This layer shows three components:
- Services - which security services need to be provided to the organization. For example, endpoint malware detection.
- Technologies - the technologies used by these services. For example, AV and EDR.
- Vendors - which vendors deliver the technologies? For example, Crowdstrike and Palo Alto.
5. Optimizing the Security Investment
It’s challenging for organizations with a limited budget or resources to know where to invest time and money best. The list of risks and threats never stops evolving, so decisions need to be made wisely.
Enterprise Security Architecture Helps Identify the Right Security Investments
All companies will have a capability or area of the business that could be negatively affected by risk. The four layers (Business, Risk, Control, and Capability) help mitigate risks and minimize a possible negative business outcome.
“mnemonic Enterprise Security Architecture is a unique way for companies to make informed business-driven decisions when making security investments.”
- Angel Alonso
Want to dive deeper? Watch mnemonic’s Security Report webinar: Enterprise Security Architecture; optimize your security investments.
Benefits of Implementing Enterprise Security Architecture
Migitating risk, being in control, and supporting the wider business are all reasons to implement Enterprise Security Architecture. Organizing the complexity of cybersecurity is essential if organizations can optimize security investments. The mnemonic team outlined benefits of using their Enterprise Security Architecture framework:
- Maximizing security ROI: ensure your organization gets the most out of the investment
- Identifying security gaps: where are your weak points?
- Minimizing the most pressing risks: what needs urgent attention from your security team?
- Becoming future-proof with a holistic security approach: planning strategically for long-term success
- Supporting business goals: connect the Enterprise Security Architecture with the wider organizational goals
Having the framework already built in Ardoq gives organizations a head start in their security work. It also opens the door for opportunities to collaborate with other Enterprise Architecture initiatives already taking place.
Find out how to use mESA as part of a mnemonic Ardoq bundle.
 Ardoq
This article is written by Ardoq as it has multiple contributors, including subject matter experts.
Ardoq
This article is written by Ardoq as it has multiple contributors, including subject matter experts.



/Logos/Ardoq/RGB_Ardoq_Logo_Stacked_White_Monochrome%201.png?width=80&height=77&name=RGB_Ardoq_Logo_Stacked_White_Monochrome%201.png)